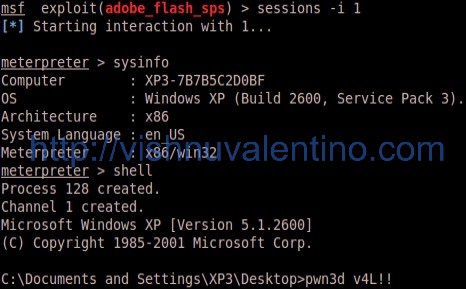
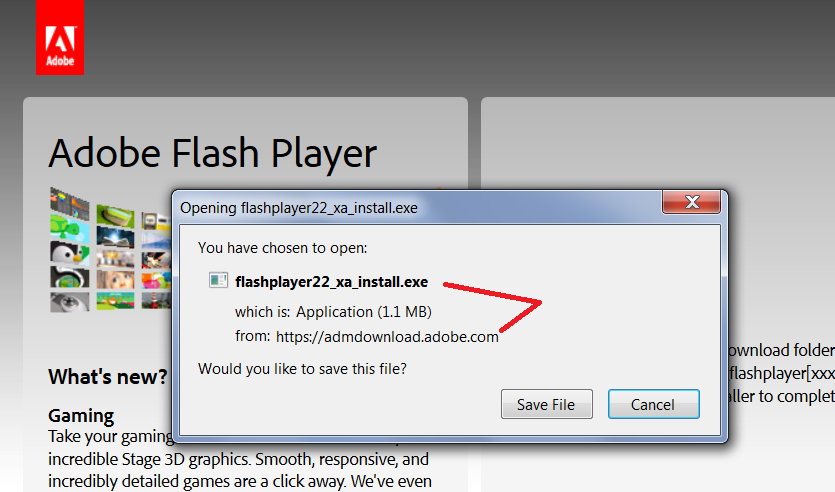
Writing Exploits for Win32 Systems from Scratch | NCC Group Research Blog | Making the world safer and more secure

Regulation & Technological Innovation: Opportunities, Challenges and Emerging Approaches | BID | Curso tutorizado

Tool Release – Web3 Decoder Burp Suite Extension | NCC Group Research Blog | Making the world safer and more secure